Every organization must invest money to keep ahead of the curve in a constantly evolving market, yet many …
Empower Your Business with Tailored IT Services & Strategic Technology Alignment
"Level up your data protection and ensure regulatory compliance with our comprehensive IT services. Our partnership is designed to not only secure your systems but also streamline workflows and deliver tangible results."






Enhanced by Leading Technology, Fueled by Superior IT Service Professionals
Meet the team that pairs best-in-class technology with sincere client partnership.
-
March 2006
Leon Hart founds ProSource Technology Solutions (PSTS)
-
April 2010
PSTS builds its own data center infrastructure from scratch
-
September 2021
ProSource Technology Solutions rebrands as ProSource
-
Today
Focusing on delivering great service and practical IT solutions
Advancing Companies with
Next-Level Technology Solutions Since 2006
succeed by tirelessly obsessing over the details.
- Mentoring the next generation
Technology moves at breakneck speed. We take the time to ensure our staff is continuously trained in order to provide the best service for our clients. - Experts in our industry
Educating our customers on how they can provide better outcomes for practice and patients in paramount to our joint success. - Fostering relationships that matter
We come to you, regardless of location, to build lasting relationships that drive positive outcomes for both parties.



Delivering IT Services & Diverse Solutions
Across Industries
For over 16 years we’ve helped our clients and employees
succeed by tirelessly obsessing over the details.

Healthcare
Technology moves at breakneck speed. We take the time to ensure our staff is continuously trained in order to provide the best service for our clients.

Manufacturing
Streamlining production processes and optimizing efficiency in the creation of goods through innovative manufacturing solutions.

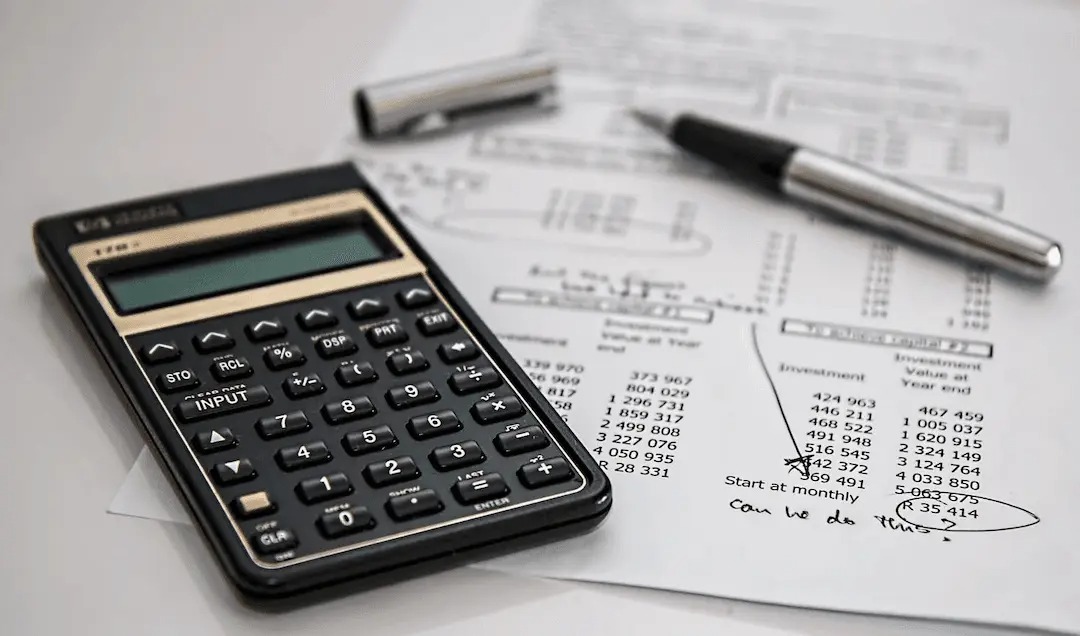
Financial Services
Providing comprehensive financial solutions and services to individuals and businesses, ensuring sound financial management and strategic planning.

Engineering
Leveraging cutting-edge technologies and expertise to design, develop, and implement innovative engineering solutions, contributing to advancements in various fields.
The latest from our IT blog
Four data backup solutions: a comparison
When it comes to data backups, there’s no one-size-fits-all solution. As such, you’ll want to consider the pros …
Common ways Microsoft Office 365 migrations fail
If you are considering moving to Office 365, you should be aware of five factors that can cause …
Speak with an IT expert
Schedule a free, 30-min consultation with one of our
IT experts — if, after the call, you didn’t get any value,
we’ll buy you a coffee!



Contact Us
Don’t hesitate to contact us
Orlando, Florida
Oviedo, Florida
- 2464 Royal Ln. Mesa, New Jersey 45463
- +1 407 955-5255
Melbourne, Florida
- 4517 Washington Ave. Manchester, Kentucky 39495
- +1 407 955-5255
Join us, we're hiring
Our team is growing fast and we’re looking for curious people like you to join us.
Copyright © 2024 – ProSource. All rights reserved | Terms & Conditions | Privacy Policy